How to Protect cPanel Servers from xmlrpc.php and wp-login.php attacks
Recently We’re seeing an increase in massive brute force attacks on WordPress installations on some cPanel server which were causing unnecessary issues which are flooding and overloading the server to the point it’s consuming all resources. It’s possible to block wp-login.php, xmlrpc.php attacks completely from the server-side rather than going into each WordPress.
let’s get started with CSF firewall
Create custom log from which CSF will be able to search for wp-login.php and xmlrpc.php requests
vi /etc/csf/csf.conf, and locate the line:
vCUSTOM1_LOG = "/var/log/customlog"
changed it to
vCUSTOM1_LOG = "/usr/local/apache/domlogs/*/*"
Once you add the line, it should look like this:

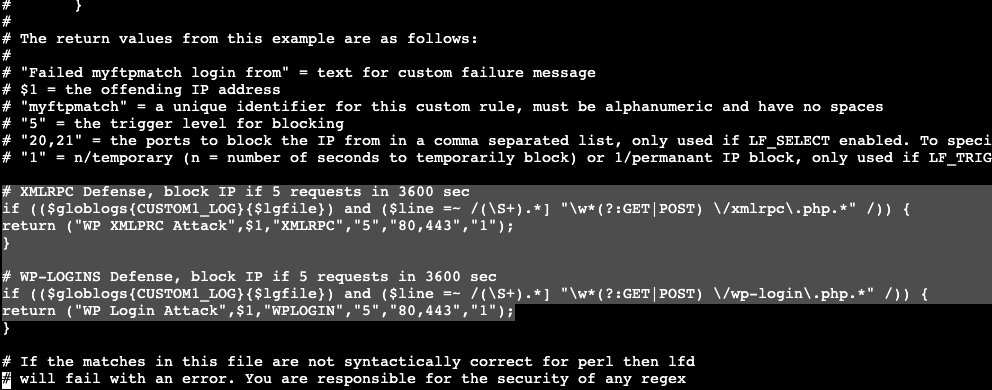
Create a custom function for CSF so it will be able to block those attacks. We will configure CSF to block the offending IP if exceeds the 5 POST or GET requests to the xml-rpc.php and wp-login.php files in less than 3600 seconds.
vi /usr/local/csf/bin/regex.custom.pm Then add this:
# XMLRPC Defense, block IP if 5 requests in 3600 sec
if (($globlogs{CUSTOM1_LOG}{$lgfile}) and ($line =~ /(\S+).*] "\w*(?:GET|POST) \/xmlrpc\.php.*" /)) {
return ("WP XMLPRC Attack",$1,"XMLRPC","5","80,443","1");
}
# WP-LOGINS Defense, block IP if 5 requests in 3600 sec
if (($globlogs{CUSTOM1_LOG}{$lgfile}) and ($line =~ /(\S+).*] "\w*(?:GET|POST) \/wp-login\.php.*" /)) {
return ("WP Login Attack",$1,"WPLOGIN","5","80,443","1");
}
Once you add the rule, it should look like this:
finally restart CSF and LFD to apply changes:
csf -r
service lfd restart
let’s get started with another solution
Prevent xmlrpc.php attacks with ModSecurity rules from COMODO Web Application Firewall
install ModSecurity Vendor Rule Sets from waf.comodo.com, these rules contain protection for xmlrpc.php attacks.
